Hacked
Introduction to Security in Web Development
James Cave and Chris Lienert introduce their talk on the importance of security in web development, with a focus on the often overlooked aspects of security in everyday coding practices.
Understanding Security Breaches
The speakers discuss the reality of security breaches and the need for awareness among developers. They highlight the gap between media-reported hacks and everyday security incidents.
Scenario-Based Learning: Developer Mistakes
They present the first scenario, focusing on a developer inadvertently committing AWS keys to a public repository, leading to a security breach and financial loss.
Real-Life Reflections on Security Oversights
Chris and James reflect on their personal experiences with security oversights, emphasizing the ease with which breaches can occur and the real-world consequences.
Scenario 2: Security Policies and Developer Frustrations
The second scenario illustrates a developer bypassing security policies to expedite work, resulting in a security breach. It demonstrates the conflict between security protocols and developer convenience.
Importance of Adhering to Security Policies
The speakers emphasize the importance of adhering to security policies, even when they seem inconvenient, and the consequences of circumventing these measures.
Scenario 3: The Consequences of Neglecting Security
In the third scenario, they discuss a fictional pirate attack as a metaphor for the consequences of neglecting security measures and practices in development.
Reflections on Security Breaches and Developer Responsibilities
Chris and James discuss the common causes of security breaches and stress the responsibility of developers to maintain security standards in their work.
Learning from Security Incidents
The presentation highlights the importance of learning from security incidents and the role developers play in preventing breaches through better practices and awareness.
Proactive Security Measures in Development
The speakers conclude by urging developers to take proactive measures in securing their code and systems, advocating for a more security-conscious approach in web development.
Chris Lienert: This is James.
James Cave: That's not you!
He's in the movie.
Chris Lienert: That is not me.
I'm sure we rehearsed this and that wasn't there.
This could be me.
James Cave: That's him.
Oh, hang on a second.
Chris Lienert: James is here because he actually knows security stuff a bit.
I'm here because I talk too much.
James Cave: He's here because he does talks.
I'm here because he roped me in.
Chris Lienert: Yeah, I've dragged him into this against his will.
He had no idea what he was in for.
We're not really security people, either.
If this was web direction secure, we'd probably be walked off the stage at some point for lack of qualification.
We're good with scenarios.
As James says, I do divs, he does hacking.
But despite being non security people, we're surrounded by it all the time, whether we like it or not.
So that kind of led us down this path for this talk to find out a bit more about it.
The talk description versus what we've actually got for you today is very different.
Because we, we learned things along the way.
This is a good thing.
Luckily, we're here to share it with you today.
The curious thing, something that started us off down this track in the first place is you see the media releases when someone gets hacked, but you don't hear about every other security incident that happens all the time.
So what happens.
Why do these breaches actually happen.
Could we have done better about it at some point.
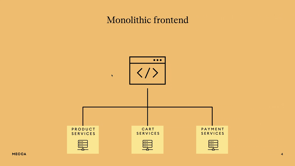
For the talk today, we'll go through three different scenarios.
Are they based on real incidents.
James Cave: Maybe.
Chris Lienert: On stage here in public, of course not, every single one is completely made up, none of these really happened.
James Cave: Not real companies.
Chris Lienert: Yeah, talk to us later on and we might be able to tell you the truth about it.
But anyway.
To scenario one, starting with a developer.
Stupid CSS, why won't these boxes line up properly.
I'll just put some extra divs in there, they fix everything.
James Cave: What divs?
Chris Lienert: All right, code, I've got my AWS key, thank you DevOps.
What am I going to do with this.
I'll get to it later on.
Ostrich Meme for Web Directions Conference.
I can't even remember if we've done this.
Did we do this, James.
I don't know if we did that one.
No idea.
Too much pressure, too little time.
All right, I'm just going to pop DevOps, the AWS keys, and just go into Todo.
We'll get to it later, because right now, we'll deal with it.
All right, I'll just save that.
Very good.
I'm going to securely close this file because I'm secure.
This is good.
Not a problem.
All right, that is there.
Good.
Now I'm ready to commit that.
Excellent.
There's my diff.
Oh, good.
Make the change.
Yes, of course.
Did I read that.
No, I did not.
What on earth is this guy doing.
Added some more divs because that's what front end programming is all about.
By the way, I run Melbourne CSS.
Spans.
Spans as well.
Alright, that's pushed, all done.
I've got other places to be.
I've not had caffeine for seconds.
I just need to get this done.
Let's push the other one.
I can't even remember what that change was.
To do whatever.
Oh yeah, it's the DevOps thing.
I'll deal with it later on.
Once it's pushed, commit early, commit often, right.
It's all good.
So I'll just shove that in there.
Didn't read that either.
All good.
We are sweet.
Oh yes, commit messages.
I hate having to write commit messages.
Some DevOps stuff, didn't even read what it was about.
Let's just march on.
All right.
Are we good.
We're good.
Excellent.
All right.
Over to our handy hacker.
James Cave: Oh yeah.
Oh, we're scanning GitHub.
Just constantly scanning.
Oh, we've got something.
Oh, here we go.
A new commit.
Oh, it's got a key in it.
Oh, that's great.
I can use that.
Let's deploy some miners.
I've got to put in his key.
Cutting and pasting is hard.
I've got to put single quotes around it.
How many.
Nine.
No, I did nine and nine.
Just get on with it.
Let's make some money.
Cool.
Got some machines up.
Making some Monero.
Is it Monero.
Chris Lienert: Monero.
I don't know.
I'm the cool kids.
James Cave: I'll just do Bitcoin.
Chris Lienert: You're the hacker.
I'm the programmer.
I don't know.
Sometime later, back to the developer.
What do you mean it doesn't work on a mobile.
It worked on my desktop.
Isn't that the same thing.
James Cave: Chris.
Chris Lienert: Yeah, I told them it worked on my desktop.
I need to talk to you about something.
I told them it worked on my desktop.
James Cave: Did you put the divs in.
Chris Lienert: Yeah, I put in divs, and when that didn't work What do we do when divs don't work.
James Cave: I need to talk to you about the bill.
Chris Lienert: We put in spans.
Bill.
What bill.
James Cave: The bill.
Chris Lienert: What bill.
James Cave: You've done some cool things, I can tell, because the bill's really big.
I want to see the cool things.
What have we got.
The bill.
Chris Lienert: Ooh, that's a bill.
This is a real screenshot, too.
What happened?
James Cave: You got owned.
Chris Lienert: I got owned.
James Cave: It happens.
A lot.
What we said at the start, most of you don't know.
Most of the time, it doesn't even get in the press.
No one even talks about it.
Script kiddies.
They're out there.
It's not meant to be mean, it's meant to be insulting.
To you, a kid with a script, their job is trivial.
They just wait for you.
And then bing!
Chris Lienert: Ding $20,000 is down the drain.
James Cave: Ding.
Bing.
No, good bing.
Good bing.
Good bing.
Chris Lienert: We're all good bing.
Alright.
Random cat picture.
Every time I present, I put a random cat picture in somewhere, because I like cats.
James doesn't like cats, so we've got a dog in here as well.
We're all about equal opportunity.
This is a problem we're doing joint presentations.
James Cave: You can tell that this is a joke scenario, but this actually happened to me.
I was doing a Petabyte size, DR moved from one system to another, from one region to another, and it was, so the costs are going to go up and down every day, massively, $20,000 a day, then down to zero the next day and up again, and it actually took, I don't know, a couple of days for us to find that I had actually, it was actually a to do file that I'd put an AWS key into, and it happened to go up into a public repo, so it does happen.
Chris Lienert: That's the thing with every single one of these scenarios is to preempt a bit.
They sound ridiculous, but every single one of these things has happened at some point.
Scenario 2.
Here's a handy developer.
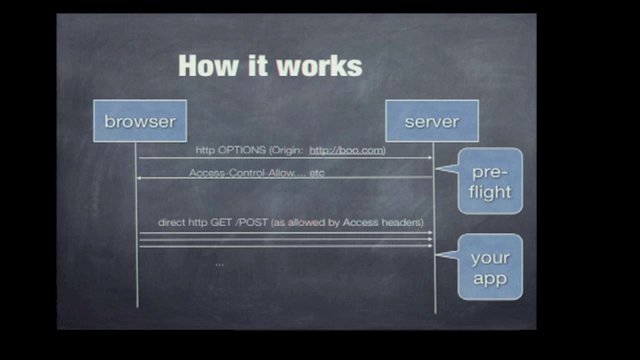
Alright, I'm trying to open port 22, denied by policy.
Ah, stuff you policy.
Security!
I just got blocked trying to open this port.
Port 22, can I do that.
James Cave: That's a secure port.
Are you have you got a risk assessment done.
Chris Lienert: Risk what.
I have deadlines.
I really need to get this done.
James Cave: Yeah, so if you can just go ahead and fill out the form, that would be great.
The form.
Yeah, your product owner needs to allocate budget, you need to do a risk assessment, you need to have a response plan for your compromise, you need to have access management, you've got to join the domain, you've got to, tags, you've got to work on your tags, buddy, you've got to, logging and monitoring, make sure that they're set up, are you using the Chris Lienert: SOE.
I'm listening to everything you're saying, this is great!
James Cave: Okay, cool we need a backdoor on it our backdoor, we, security always puts a backdoor on stuff so that we can log in and break it whenever you're asleep.
Do you have a ticket number.
Chris Lienert: Yeah, it's all good.
Cheers.
Thanks.
All right.
I'll just change the port to 1022.
That's completely different.
All right.
Permit root login.
Prohibit password.
We don't want that.
It's going to be too hard.
Let me change this to I want that to be yes.
Delete.
Thank you.
Now I can log in as root, except one more change to make.
Where are we?
Password authentication is currently set to yes.
Thank you.
Done.
Perfect.
Push the code out of here.
Thank you very much.
Over to our hacker.
James Cave: All right.
I want to do a custom scan today.
I'm just going to play around a bit.
I'm going to I've got an EC2 instance here that I've taken over earlier.
Let's look at Ah, the whole 16, sure.
Random ports, 80, 80, 80, 80, 20, 80, 20, 10, 80, 22, 2, 2, 2, 10, 22.
No one ever used that.
Scan it.
Shouldn't take long.
Might take a long time.
I'll just wait around.
Oh, got something.
SSH4.
Cool.
Brute force attacks.
Might have used a password.
Ah, just drop it in.
See how we go.
This is how it works in the movies.
Did you do a strong password.
Chris Lienert: Every password's strong.
James Cave: Always.
Chris Lienert: It's the same one every time, so I don't know what you mean.
James Cave: Oh, hello!
Oh, cool, I've got something.
Oh, root password, sweet.
Let's make some money.
And just drop it.
Port, root, he put a special character into his password.
So I guess I will put it in single quotes.
FTT, is that any good.
Bitcoin.
We're still doing Bitcoin.
Yep.
Sweet.
Making money.
Thanks, Chris.
Deep guy.
Chris Lienert: You don't know who I am.
James Cave: I don't know who you are.
Chris Lienert: Back to security.
James, do we care about traffic on port 1022.
Copy.
James Cave: Sorry.
No, we don't care about port that, that traffic.
That's not a secure port.
Don't worry about it.
Chris Lienert: Alright, James Cave: no worries.
Cheers.
There's no alerts, don't worry about it.
Chris Lienert: What happened.
James Cave: You jumped over the gate, rather than opening the gate, going through it, and closing the gate.
You're under pressure.
You don't need roadblocks.
They were dumb roadblocks anyway.
Chris Lienert: It's a stupid security policy.
I've got work to be done.
James Cave: You're clever enough to go around.
You are.
You're all clever enough to go around the roadblocks.
But they're there for a reason, and it doesn't take much.
If it's too hard to get it set up with your proper centralized auth, you're not allowed to make it local accounts, right.
So fine, just enable auth on root and keep it simple.
Password auth on root.
Why not.
Chris Lienert: I fixed the problem.
The other thing that went wrong here was the security were monitoring the things they were meant to monitor.
They weren't looking at the things they're not meant to monitor.
James Cave: Oh yeah, what else happened.
Oh yeah, the other bit.
Security is not monitoring everything.
There's just too much going on.
If you find a way through the policy, you're not a winner, you're a cheat.
There was another way, you just didn't bother to find it.
Security is in an arms race with the bad guys.
Don't make their life harder.
Try and find, don't, by trying to find ways around them.
Work with them.
Alright.
Chris Lienert: More cat pictures.
I had to watch this several times over to work out it's not actually the same cat as well.
James Cave: So I have another random tidbit.
People do this all the time when you're trying to find ways around things.
If you proxy egress through some old random VM that you got lying around, you're not saving time, you're breaching policy.
Policy is there for a reason.
Don't gamify ways around it.
Chris Lienert: All right, enough cats.
Scenario three.
This one's pretty heavy.
So we're somewhere in the Caribbean.
James Cave: Naval Lieutenant.
Chris Lienert: Naval Lieutenant, thank you.
And you were in the army too.
Monday the 22nd of May.
James Cave: I'm a watchman.
Chris Lienert: Sailing well, crew morale is high, although I'm worried the night watch is falling asleep on duty.
You awake, James.
James Cave: Yes.
Chris Lienert: Next day.
Tuesday the 27th, 23rd of May.
23 follows 22.
Found both watch asleep.
I've reprimanded them.
James, wake up.
Don't do that again.
James Cave: Sorry, sir.
Chris Lienert: Hope that's the end of it.
Later that night.
I don't have any props for this one, actually.
Actual pirates.
We've been, we're ready to board the frigate, I can't even read now.
We've been tracking for days, the night watch are asleep every single night.
Time is absolutely now.
James Cave: Watch me.
Chris Lienert: Here, mate, can I take that.
Cheers.
The next day.
Wednesday, the 24th of May, the ship has been raided during the night.
Everything is gone.
The nightwatch have been spoken to.
And they said they won't fall asleep again.
So it's all sorted.
Great.
What happened.
Don't leave my wallet there.
We had known bad practices.
We had people literally asleep on their job.
James Cave: Dude, they were pirates.
They stole everything.
Chris Lienert: That's the problem, isn't it.
James Cave: Oh, I probably should have been watching for them.
Chris Lienert: If only we had something.
james: I only work here.
If you accept bad practices, then they become entrenched.
If you ignore the recommendations, the hackers are going to get ahead of you.
James Cave: You need to work at this.
You need to accept responsibility for old school bad practices and just stop doing them.
You need to understand policy, what the warnings are, what the risks are, what the vulnerabilities are, and understand some security controls.
A lot of the time, you are actually in control, and you can't excuse the ostrich method.
We were talking about that earlier.
Chris Lienert: We did have a reference to the ostrich method.
Head in the sand is not a good place to be.
James Cave: If you know it shouldn't be done, stop doing it.
Chris Lienert: The things have changed, and this is the thing.
So what we've gotten away with in the past, you can't anymore.
Back in 2005, people started actually running random bots to check open ports on servers.
And back then, when I was working, because I'd been around too long part of my job was actually checking the logs every day to look for unusual traffic, because one person could do that back then.
And it changed.
We couldn't actually leave things open anymore because you would get done at some point.
We saw GitHub scanning before.
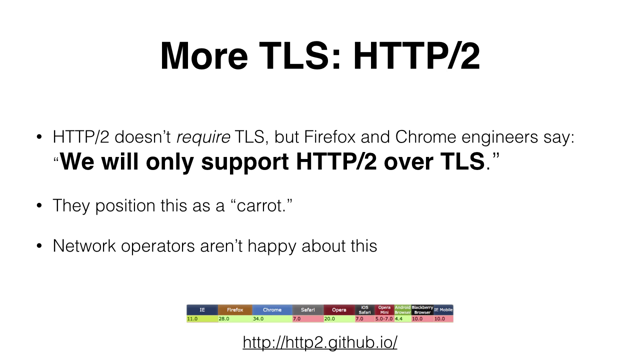
James Cave: It used to be 48 minutes, and now it's down to less than 10.
You put an AWS key into a public GitHub repo, then you are owned 8 minutes.
Chris Lienert: Which is insane.
I'm glad I haven't been caught doing that.
James Cave: Wait a minute.
Chris Lienert: When we started researching this talk, we had two major questions.
One was, who are the attackers.
And why are they trying to breach us.
James Cave: We could have talked about the vulnerabilities, and the supply chain, and the secrets in the code, and we could talk about the hackers, and the hacker's motivation.
Chris Lienert: Are they Russian.
Are they script kiddies.
Are they going for fun.
James Cave: We could scare you and say words like nation state actors, and advanced persistent threats.
Chris Lienert: But in the end, it doesn't actually matter.
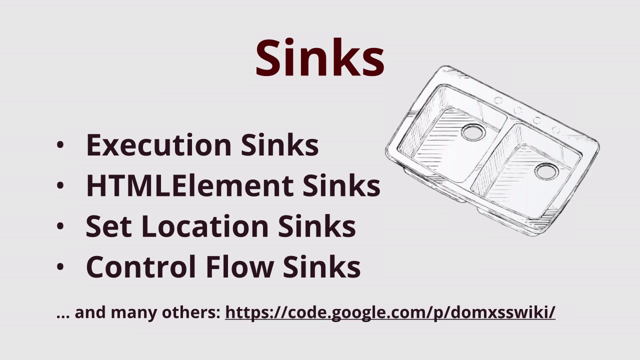
James Cave: We could talk about attack vectors and how the baddies go from taking your bearer token.
Chris Lienert: But it doesn't matter.
James Cave: That doesn't matter.
You'll get hacked.
Chris Lienert: If you leave something vulnerable, you'll get hacked.
It doesn't matter what their motivation is, you'll get hacked.
It doesn't matter what they take, you'll have been hacked.
You'll have lost whatever you've lost because you left the gate open in some way.
You allow it to happen.
You're done.
And when you are breached, you can't be unhacked.
Especially when it goes bad.
That reputational damage is awful.
Were you working at unnamed telecommunications company at some point in the last 18 months at any point.
And what's your job title again.
What were you doing there.
James Cave: Just a developer.
I didn't have anything to do with it.
Chris Lienert: You left not long afterwards.
That's great, isn't it.
James Cave: Oh yeah, I did, yeah.
I had nothing to do with it.
It doesn't matter.
It doesn't matter whether you had anything to do with it or not.
If you're, if the company that you work for is hacked, it impacts you.
Even if, whether it's Medibank and you don't even work for them, it still impacts you.
Chris Lienert: Unnamed healthcare provider.
James Cave: Didn't happen.
Don't know anything about it.
It doesn't matter.
It affects all of us.
It affects you and it affects the security people and it affects the public.
Chris Lienert: We're trying to put across here, hopefully, the severity of what you're dealing with.
Again, your whole career can be tarnished because you get done.
Even if you had nothing to do with it.
You're somewhere in the realm and yeah, you're done.
And one of the problems with this is media portrayals.
This is ABC.
I love ABC.
But we see this over and over again.
This is a recent Four Corners thing that was done.
Chatting with a hacker.
Oh wow, they found a Russian.
Hackers have their own custom usernames.
I'm "cleaner".
They have teams with weird names.
It's yeah, we've got Interstellar.
They get bonuses for completion of work.
You've never had that at a startup before.
Completely alien and different from the rest of us, except they're exactly the same as us.
They're us.
The difference between us and the hackers is nothing.
James Cave: They're just as clever as you.
Chris Lienert: Turning up every day doing their job, except they're penetrating our work.
This doesn't help at all.
Anyone who's in the media, please tell your journalists.
I mean, Ars Technica recently asked, is cyber security an unsolvable problem.
We answer, yes, and that's our time.
Thank you.
Oh, wait, I've got more.
James Cave: Ten minutes.
Chris Lienert: Five.
James Cave: So why are we here.
Because we want you to know that you can make a difference.
And it will be good for you, and less bad for you.
It doesn't matter what their motivation is.
Is it money?
Chris Lienert: Is it fun?
James Cave: It doesn't matter.
They're still going to hack you.
Chris Lienert: But what can we do about it.
We can learn.
James Cave: We can learn.
What can you do.
You can learn about the risks that you're up against.
It's not really that hard.
You know you're sanitizing input.
So learn prompt engineering.
If you want to talk to the bots.
Learn about the risks with the things that you do.
If React, learn about what security risks exist with React.
Chris Lienert: If you've got a blocked port, why is that port blocked.
Why are we blocking port 22.
Ask those questions instead of trying to fight it.
It's better to know what you're doing and what you're up against rather than trying to work your way around it.
But then, once you've learned James Cave: What can you do.
Just do something.
Don't be an ostrich.
We never put that meme in.
Chris Lienert: No, we didn't.
James Cave: Actually, they're tending their underground nests, so it's not really putting their heads in the sand.
It is, but, denial isn't a noble response.
Do something that makes you better at what you do because you do it more securely.
Do the hard bits as well as the fun bits.
That's really the only thing you can do.
Chris Lienert: But we looked at incident response before with Hila's Talk.
James Cave: If you don't have these things in place, and you don't do things better than you did them yesterday, and better than the hackers will do, the baddies will keep getting better.
They will do stuff.
They will do a bunch of stuff.
If you stay ahead of them doing the things that you do, but knowing that if you don't do it well, they will get ahead of you.
Chris Lienert: And then once you're done doing things, you can do more, you can be a champion.
James Cave: Understand the rationale for security practices and share them with people.
Understand why you're doing something and actually talk to people about doing it.
I see clever developers finding holes through security controls and being proud of it.
Stop being proud of finding your way around the gate.
Find the way through the gate, do it securely, and share that.
Please.
Chris Lienert: You'll notice, especially as we get into this heavy part of the talk, there's a bit of fire behind what we're talking about here.
And I don't do shows of hands in Australia because we're not very good at participating in things, but there's a good chance that most of you in this audience have been victims of some kind of PII breach in the last 12 months, two years.
I've been done multiple times.
I get random calls at least once a day.
I love it.
Thank you very much.
Unnamed providers of different things.
But the people responsible for those hacks, yeah, you've got bad actors there, but the ones who allowed them to do things are us.
We're the ones who can make the difference.
So walk away from this talk knowing that you know that you need to do better.
You need to actually put things in place and you can make a difference.
You can stop your company being done, even if you don't care about your clients or letting James talk.
James Cave: It affects your career too.
These things have a true impact on you.
If your company gets hacked, it's on your resume.
Oh, you worked at Chris Lienert: Unnamed telecommunications provider.
James Cave: I could have.
Yep, but it wasn't me.
It has real impact on you.
It has, whether it's you as a member of the public, or whether it's you as a developer who just happened to be involved in something that was anywhere near it.
Security breaches happen.
You do get hacked.
And it's up to all of us to actually do something about it.
Chris Lienert: Yeah, but at least make it harder.
If you go by media releases, security breaches don’t happen that often. In practice, there are many incidents that no one ever hears about and sooner or later it’s going to happen to you.
What happens when you get hacked? We’ll go through different scenarios and discuss what you can do about it.